A recent study by KPMG on federal cloud adoption reveals main drivers, demotivators and tips for what to look for in a cloud hosting provider for both private and the public sector. The study reported findings on governments, citizens, cloud service providers and IT leaders.
A recent study by KPMG on federal cloud adoption reveals main drivers, demotivators and tips for what to look for in a cloud hosting provider for both private and the public sector. The study reported findings on governments, citizens, cloud service providers and IT leaders.
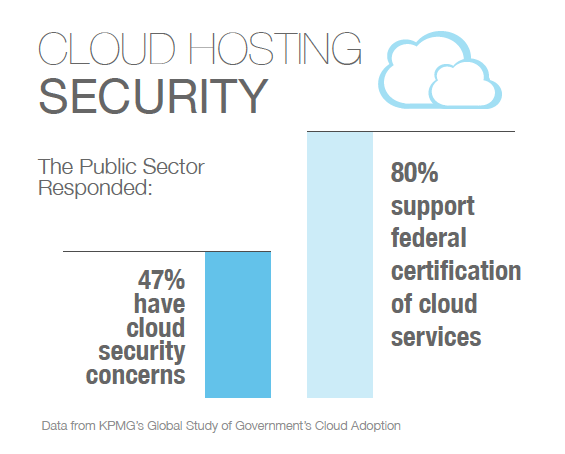
Security is a major concern when it comes to the cloud, but certification could help – while 47 percent of government respondents cite security as their most significant concern, nearly 80 percent claimed they would be more confident if cloud services were certified by a government entity.
Cost is the main driver for both government and the private sector to move to the cloud, with 73% and 75% respectively claiming it was necessary to realize cost reductions and savings in order to move to a cloud environment.
But how significant would those savings need to be in order to make the transition? At 43%, the private sector only needs 1-10% reduction in IT or non-IT costs to switch over, while the public sector appears to be confused, with 29% claiming they didn’t know what percent reduction in budgetary costs they needed in order to make a cloud decision.
In addition to cost, technical drivers, such as flexibility, scalability, simplicity, security and advanced technology, were ranked as either important or extremely important by 79% of government respondents, and likewise by the private sector.
Strategic factors, such as process transformation, linkage to business/organization partners, speed to market/implementation and a focus on core competencies were ranked as important or extremely important by 77% of private businesses. This extends the benefits of cloud computing to a broader business perspective as companies prepare for long-term growth and reorganize priorities in order to realize increased efficiency.
What does a government (and as should any company concerned with security) look for in a cloud provider? Dave McClure, Associate Administrator of the Office of Citizen Services and Innovative Technologies at the U.S. General Services Administration (GSA) lists a few:
- “Cloud service providers face a long and tough accreditation and authorization process” including an assessment of access controls and tests to determine the level of knowledge a cloud provider has about relevant potential risks.
- Continuous monitoring with real-time alerts instead of post-breach audits is important in order to be “on top of any breach as fast as we can be,” according to McClure.
- For optimal security, multiple levels of technical controls, operational controls and policy controls are necessary to eliminate risk from all angles. Similar to the pillars of HIPAA safeguards that require policies regarding administrative, technical and physical security, complete data protection requires vigilance and cohesion in many different areas of an organization.
- McClure also is concerned with the managed cloud – he says he is looking for providers that have a clear vision when it comes to integrating and managing the cloud within a legacy environment, more commonly known as hybrid clouds. Hybrid clouds integrate different types of IT infrastructures to support a highly customized IT environment with cloud servers used to support some services but not all.
The study provides some excellent closing insights/tips for a range of professionals, including government leaders, government IT professionals, cloud vendors and more. Recognizing the new security challenges presented by the cloud, the study advises government leaders (or business leaders) to find an effective and accurate way to audit several areas under the cloud, including:
- Internal audits
- Global security
- Regulatory implications of data privacy
- Storage, colocation and more.
The study urges professionals to ask the following questions as they navigate the cloud vendor selection process:
- How can you ensure all regulatory requirements are met?
- What internal controls over data security need to be implemented?
- How will the data breach/disclosure process play out?
- What is the process for sharing data encryption keys internally and with a vendor? etc.
For more on the cloud, check out our comprehensive Cloud Wiki and our informative Cloud Computing E-Tips.
References:
KPMG Global Study of Governments’ Adoption of the Cloud (PDF)